InvizBox 2 research and investigations as the company seems to have abandon the product. Note 2021-02-25 - this page and research is a work in progress.
Introduction + InvizBox Company Fails
InvizBox “company” appears to have abandon software updates for InvizBox 2 devices. For example, the Model 2 home/office WiFi router device.
-
This “company” still ships devices, but their overall business is in a state of disrepair, as far as I can tell.
-
They still respond to emails regarding shipping or general questions, but the responses are not impressive to me.
-
Their online shopping “cart system” is in a major state of brokenness. Their cart system does not accurately differentiate between one time purchases for physical products and recurring subscriptions for network services.
-
Their shopping cart system asks for a “billing address”. This is requested even if Cryptocurrency is the selected payment method. It is obviously only needed for a credit card payment method.
-
Their shopping cart system DOES NOT ALLOW OR ASK for a Delivery Address for physical products. I am COMPLETELY baffled as to how they have been able to effectively operate a “business” with this broken system. How can all customers be expected to provide a single address for both billing and delivery? This is highly unusual, and perhaps something I would expect to see in year 1997. But I imagine that even Amazon in 1997, made a process to let customers provide an address for billing and delivery. (Amazon has for many years now)
Missing obvious capabilities of InvizBox 2 Device
Below are the three main features missing from InvizBox 2 device:
-
Being able to add your own personal “custom” OpenVPN servers /tunnels via the Web GUI admin portal.
-
Being able to add Wireguard VPN servers /tunnels via the Web GUI admin portal.
-
Being able to drop the horrible Windscribe VPN provider, and configure another commercial VPN service provider through the WebGUI admin portal. I would also be satisfied if this was easy to do via the command line interface.
-
I would also be satisfied if there was a straightforward way to do anything through ssh access to the device using the command line interface.
-
However, thus far, my attempts to add a known properly working, custom OpenVPN that I created via the command line interface, are futile. It does not connect properly.
- There does not seem to be an obvious way to disable
torfrom running on this device, EVEN IF you have no networks configured to use it! Tor is always running, and evenopkgpackage manager is configured to download OS updates via a .onion domain name.
I looked in the Web GUI Admin Portal and saw no option to disable tor.
Next I removed execute bit from startup script file tor in directory /etc/init.d. I then rebooted,
and the device seemed totally unusable /bricked, so I had to factory reset yet again. The main reason
I want the option to be able to disable tor, on the device, even if a pain to do so, is that there is a CPU and bandwidth penalty of sorts for running tor on a small embedded device like this when the clients are mostly not using tor on a daily basis. In my opinion, this should be something the end-user can turn on or off as they choose, not be forced to always have it on. End-users in lower bandwidth situation, might only want a VPN tunnel, and this would increase overall bandwidth demands for no good reason.
Main Issues regarding lack of Wireguard capabilities
What I have noticed is that package wireguard-tools can be installed without issue on this
device with to problems. However, the main wireguard package, which needs a Linux kernel module, can not
be currently installed properly.
Via the opkg package manager:
- I can install some non-architecture specific packages, like
htopandzsheasily. - I can install some packages that are more specific, like
nanoas well. - But when I try to install
wireguardpackage,opkgclaims there is a missing dependency,kmod-wireguard.
And I can see that this package does not exist in the OpenWRT repository for the 21.02 release of arm_cortex-a7_neon-vfpv4
architecture.
Debugging Wireguard Installation on InvizBox 2 Linux Device
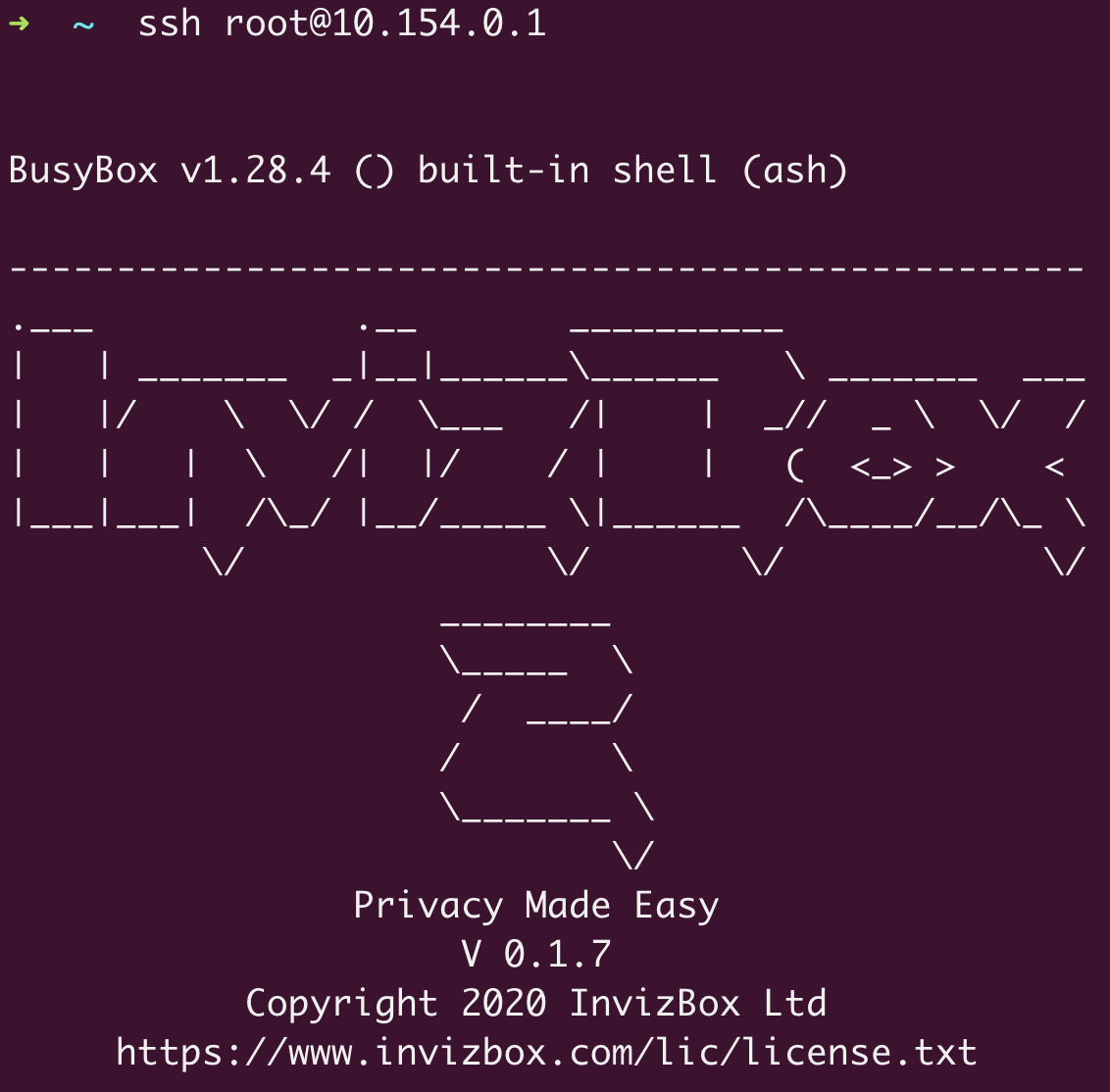
InvizBox 2 Firmware Version: 0.1.7
Printing basic information about the state of the device
root@invizbox2:~# uname -a
Linux invizbox2 4.14.171 #0 SMP PREEMPT Thu Feb 27 21:25:59 2020 armv7l GNU/Linux
root@invizbox2:~# cat /etc/openwrt_release
DISTRIB_ID='InvizBox-OpenWRT'
DISTRIB_RELEASE='0.1.7'
DISTRIB_REVISION='r7989-82fbd85747'
DISTRIB_TARGET='sunxi/cortexa7'
DISTRIB_ARCH='arm_cortex-a7_neon-vfpv4'
DISTRIB_DESCRIPTION='InvizBox-OpenWRT 0.1.7 r7989-82fbd85747'
DISTRIB_TAINTS='no-all no-ipv6'
root@invizbox2:~# cat /etc/openwrt_version
r7989-82fbd85747
Set “custom” feeds repository to point to OpenWRT 21.02
cat /etc/opkg/customfeeds.conf
# add your custom package feeds here
# src/gz example_feed_name http://www.example.com/path/to/files
src/gz 21.02_base https://downloads.openwrt.org/releases/packages-21.02/arm_cortex-a7_neon-vfpv4/base
src/gz 21.02_packages https://downloads.openwrt.org/releases/packages-21.02/arm_cortex-a7_neon-vfpv4/packages
---
root@invizbox2:~# opkg install wireguard
Installing wireguard (1.0.20201112-1) to root...
Downloading https://downloads.openwrt.org/releases/packages-21.02/arm_cortex-a7_neon-vfpv4/base/
wireguard_1.0.20201112-1_arm_cortex-a7_neon-vfpv4.ipk
Collected errors:
* satisfy_dependencies_for: Cannot satisfy the following dependencies for wireguard:
* kmod-wireguard
* opkg_install_cmd: Cannot install package wireguard.
---
root@invizbox2:~# opkg install wireguard-tools
Installing wireguard-tools (1.0.20200827-2) to root...
Downloading https://downloads.openwrt.org/releases/packages-21.02/arm_cortex-a7_neon-vfpv4/base/
wireguard-tools_1.0.20200827-2_arm_cortex-a7_neon-vfpv4.ipk
Configuring wireguard-tools.
---
root@invizbox2:~# opkg list-installed | grep guard
wireguard-tools - 1.0.20200827-2
---
https://forum.openwrt.org/t/solved-info-issues-installing-kmods-on-6984-fa0275b/14872/3
---
root@invizbox2:~# opkg --force-depends install wireguard
Package wireguard (1.0.20201112-1) installed in root is up to date.
---
root@invizbox2:~# opkg list-installed | grep guard
wireguard - 1.0.20201112-1
wireguard-tools - 1.0.20200827-2
---
root@invizbox2:~# modprobe wireguard
failed to find a module named wireguard
---
root@invizbox2:~# lsmod | grep -i guard
---
root@invizbox2:~# opkg --force-reinstall --force-depends install wireguard
No packages removed.
Unknown package 'wireguard'.
Collected errors:
* pkg_hash_fetch_best_installation_candidate: Packages for wireguard found,
but incompatible with the architectures configured
* opkg_install_cmd: Cannot install package wireguard.
---
root@invizbox2:~# opkg print-architecture
arch all 1
arch noarch 1
arch arm_cortex-a7_neon-vfpv4 10
End
Notes from x86_64 Linux Cloud VPS Server (Ubuntu 20.04)
root@cloud:~# uname -a
Linux localhost 5.4.0-65-generic #73-Ubuntu SMP Mon Jan 18 17:25:17 UTC 2021 x86_64 x86_64 x86_64 GNU/Linux
cat /sys/class/net/wg0/mtu
ufw allow 61951/tcp
ufw allow 61951/udp
ufw route allow in on wg0 out on eth0
ufw route allow in on eth0 out on wg0
ufw status
Links that may be useful in the future
-
https://github.com/klenQ/Wireguard/blob/master/wireguard_openwrt.sh
-
https://raw.githubusercontent.com/klenQ/Wireguard/master/wireguard_openwrt.sh
-
https://casept.github.io/post/wireguard-server-on-openwrt-router/
Misc. Wireguard Module Notes for standard Linux distributions
In a blog post announcing Ubuntu 20.04’s arrival Canonical stated:
WireGuard is included in Ubuntu 20.04 LTS
This has been met with confusion because Ubuntu 20.04 ships with Linux Kernel 5.4, and Wireguard is officially in Linux Kernel 5.6. Canonical backported the Wireguard kernel module into 5.4 for Ubuntu 20.04
The proof is in the pudding:
modprobe wireguard # executes successfully
You can verify the wireguard module is available:
find /lib/modules/$(uname -r) -type f -name 'wireguard.ko'
You can verify the wireguard module is loaded:
lsmod | grep wireguard